Finally, there are also crypto wallets which are linked to the web (hot wallets), and similar to crypto exchanges, this sort of wallets is also vulnerable to possible hacks. Regarding the buying and selling effectivity, crypto change is a quantity of steps ahead of crypto wallets. Keeping your cash on the exchange allows you to shortly trade currencies without the necessity to deposit your funds in a trading avenue since they’re already there. While we use common wallets to store cash, crypto wallets don’t really retailer cryptocurrency.
Users can take essential precautions to guard their investments from undesirable entry and potential security breaches on exchanges by transferring their cryptocurrency holdings to a personal pockets. This pockets can be a hardware wallet for max protection or a cellular wallet or software pockets for ease of use. So, quite so much of demands are met by the diversified community of cryptocurrency wallets, ranging from protected asset storage to high-frequency trading.
Blockchain Schooling
Custodial wallets provided by exchanges, by which the change retains the personal keys, oppose this management. Users must belief the exchange’s security protocols and tips in these situations. Unlike a conventional bodily wallet that holds your money, a crypto pockets operates completely differently. It doesn’t retailer your digital foreign money in a tangible form; as a substitute, it securely stores your personal key. The benefits of utilizing a crypto wallet lengthen beyond security to include management and direct transactions. By managing one’s non-public keys, users retain full control over their funds, eliminating reliance on third-party entities.

Crypto transactions facilitated by exchanges provide speed and liquidity, making them essential for dynamic trading. Cryptocurrency wallets and exchanges are two essential tools that permit this revolutionary digital industry to operate properly. A number of wallets and exchanges are managed by the same companies, and this typically causes confusion about their differences. This guide aims to clarify the distinction between crypto pockets and exchange in addition to recommend a quantity of alternatives for every. In most cases, transferring property from a custodial service like Coinbase to a self-custody wallet like BitPay is so simple as sending crypto from one address to another.
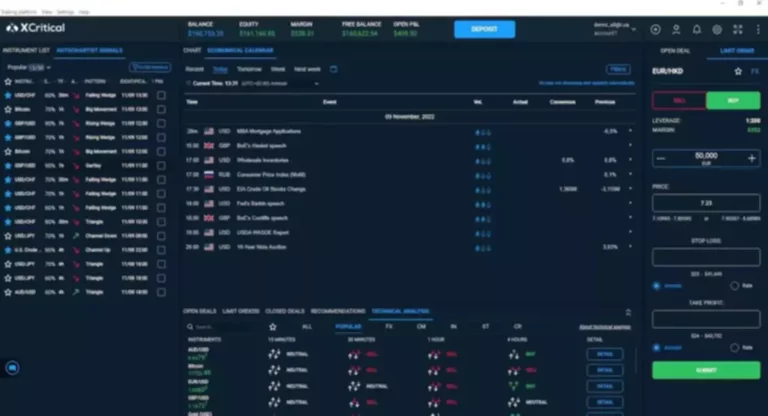
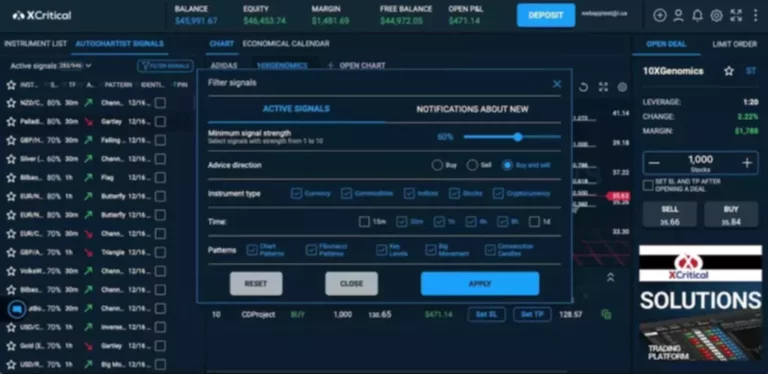
Recommended Exchanges
Throughout crypto history, there have been numerous well-publicised trade hacks which have value large sums of cash. Consequently, in comparison with utilising a private pockets, using an change carries a higher danger of safety breaches even though it may be more handy for buying and selling. To choose between a DEX and a CEX, one must weigh factors like control over digital belongings, security, and ease of usage. When selecting an trade, customers should do intensive research, think about their unique wants, and assess their danger tolerance.
While change wallets lure customers with lots of conveniences, they arrive with safety dangers. Additionally, the exchange has control of your assets, that means they may freeze your account for numerous reasons. That’s why it’s essential for customers to confirm they are sending the correct asset to the correct handle. For example, customers should ship Bitcoin (BTC) to a Bitcoin pockets tackle and Ethereum (ETH) to an Ethereum wallet handle.
One Of The Best Non-custodial Crypto Wallets
The operation of cryptocurrency exchanges involves a simple strategy of placing orders to buy or promote cryptocurrencies. Users can navigate via the platform’s interface to execute trades based on present market costs. Exchanges provide a wide range of cryptocurrencies, providing users with ample choices for asset diversification. The common consensus relating to the very best security of crypto property is storing them in an offline location that hackers can’t entry and makes you the one one liable for them. Meanwhile, crypto exchanges might work just nice should you’re not holding your cryptocurrency or don’t have giant funds that you’d be afraid to lose. Crypto wallets provide you with full control over your non-public keys, additionally presenting full ownership of cryptocurrency on that specific wallet.
You must also verify the safety features offered by the wallet, similar to backup, multi-sig, and others. However, with an change, you should ensure that the platform is regulated, offers good safety protocols, and is reputable within the business. Most wallets are limited to primary transactions, corresponding to sending and receiving cryptocurrencies.
Additionally, crypto wallets facilitate peer-to-peer transactions, enabling customers to ship and receive funds immediately, with out intermediaries. Depending on their goals and actions, users should choose between utilizing a crypto exchange and a wallet. Because of its improved security features, a hardware pockets or a software program wallet is advised for the long-term safekeeping of digital currency.
How Does A Crypto Trade Work?
Deciding the place to store crypto assets is important for any investor, as properly as balancing accessibility and security. So, it’s essential to know how crypto wallets and exchanges differ in the crypto world. Comparing cellular wallets to software wallets provides insight into the varying levels of convenience and safety available.
Centralized exchanges are operated by corporations that present a platform for users to trade cryptocurrencies with one another. A centralized exchange is an middleman that matches buyers’ and sellers’ orders. While coins bought are credited to you on the trade platform, in distinction to utilizing a wallet crypto wallet vs exchange, you are not totally in management of your belongings until you truly withdraw them to your own wallet. Using exchanges that also act as wallets still make you weak to fraudulent exercise.
Ease of use and accessibility vary between wallets and exchanges, catering to different person preferences and requirements. Wallets prioritize safety and control, typically sacrificing convenience for enhanced protection. Exchanges, then again, prioritize accessibility, offering seamless buying and selling experiences.
For enhanced security and possession, it is strongly recommended to maintain your Bitcoin in a wallet, preferably a cold pockets, rather than on an change. CEX applications are good for beginners or those that prefer a extra regulated setting with customer support. Also, CEXs have extra advanced buying and selling options such as margin trading, futures trading, and stop-loss orders. However, since CEXs are sometimes subjected to stricter regulations, it could possibly trigger delays in the transfer and withdrawal of funds. Users should consider their cryptocurrency strategy — focusing on long-term holding or frequent trading — to decide which option best suits their needs.
How Secure Are Crypto Wallets Compared To Crypto Exchanges?
In simple phrases, similarly to the stock trade, crypto exchanges are the place consumers and sellers meet. Generally, it is safer to maintain your crypto in a wallet, particularly a chilly wallet, as it provides greater management and security compared to an change. Though wallets and exchanges present some similarities, there are vital differences between the https://www.xcritical.com/ 2. Exchanges supply a range of digital currencies for buying and selling in addition to offering the infrastructure required to complete crypto transactions quickly. Owning funds is one factor, and understanding the method to manage it is a completely completely different however however essential aspect.
Some, like the BitPay Wallet, come with added advantages of a free crypto debit card, alternative to turn crypto into gift playing cards, plus different methods to spend crypto. That would not solely mean remembering your keys, however maintaining other security measures, like back-ups, updating hardware frequently, and so forth. Not owning private keys means that you are not the true proprietor of your crypto coins – as a substitute, you permit a 3rd get together to regulate what you are capable of do along with your cash. Finally, there’s also a wallet tackle – a shortened, easier model of your public key – that you can use to obtain funds. They are unique to each pockets and are one thing that allows you to work together with blockchains.
Komodo Wallet is a non-custodial wallet, decentralized exchange, and crypto bridge all rolled into one app. For instance, in 2018, one of many high 20 exchanges in the world, Coincheck, lost around $534 million worth of digital belongings, which is also one of the largest crypto hacks ever. With this knowledge, customers could manage their digital currencies safely and successfully and may make knowledgeable choices. Wallets can supply fixed access however might require technical steps for transactions. Exchanges typically simplify access but could have downtime during maintenance or excessive traffic. Your technical comfort stage ought to match the interface and functionalities of the wallet or exchange.
While we may obtain compensation from a number of the merchandise we evaluation, you don’t incur any additional cost whatsoever for utilizing our content and clicking external hyperlinks. CFDs are complex instruments and come with a excessive threat of shedding cash rapidly because of leverage. You ought to contemplate whether or not you perceive how CFDs work and whether you’ll find a way to afford to take the high danger of shedding your money. It’s a purely personal alternative that everyone getting familiar with the crypto world has to make.